Risk Management in Technology
Are you doing your best to keep your data secure?
On March 6, this year, more than 200,000 credit card details from top Asian banks in Malaysia and several other nations were stolen and put up online. This is not the first–time cybercriminals have targeted the banking industry. In early 2018, Bank Negara Malaysia (BNM) released a statement on how a security incident related to unauthorized fund transfers was detected. Such incidents gave birth to Risk Management in Technology, Malaysia, on September 5, 2018. It is a framework proposed and enforced by the Central Bank of Malaysia, i.e., BNM, to build secure cyberspace for numerous financial institutions across Malaysia. This includes those in Kuala Lumpur, Ipoh, Penang, Malacca, and various other locations.
The team of experts at EC-Council Global Services (EGS) helps you comply with the regulation and offer various security solutions to fulfill the RMiT requirements through vulnerability management, privileged remote access, and identity and access management.

What Is Risk Management in Technology (RMiT)?
Financial institutions are a consistent target for numerous forms of cyber threats from internal and external sources. Their heavy dependency on technology supports business operations, which in turn, processes copious amounts of critical data every day, but it also highlights the severity and urgency of the security risks. So, to combat the rise in cyber threats against the nation’s financial systems, Bank Negara Malaysia (Central Bank of Malaysia) built a Risk Management in Technology (RMiT) framework – RMiT BNM/RH/ED 028-11 regulation. The Risk Management in Technology, Malaysia, framework ascertains that the national banking entities understand the importance of sensitive data and protect them from nation-states, APT groups, and independent threat actors.
The regulation is designed to –
- Promote the protection of sensitive customer data.
- Promote the protection of IT systems of regulated entities.
- Ensure that each affected enterprise assesses its risk profile.
- Implement a robust program dedicated to addressing the cyber risks
- Certify enterprises in compliance with the regulations by senior management.
Now that the regulation is in force, the financial institutions are not left with any choice but to understand the framework’s requirements and comply with them.
Which Organizations Need to Comply With Risk Management in Technology Malaysia Framework?
As per RMiT, financial institutions are licensed banks, investment banks, Islamic banks, and a few other related financial institutions. The detailed list covers –
| Licensed banks | Licensed investment banks |
| Licensed Islamic banks | Licensed insurers, including professional reinsurers |
| Licensed takaful operators, including professional retakaful operators | Prescribed development financial institutions |
| The approved issuer of electronic money | The operator of a designated payment system |
The need for risk management technology in financial services gave rise to the RMiT framework. It protects the integrity of the network infrastructure of all the above-stated institutions.
Apart from that, RMiT applies to all the data centers maintained and operated by Malaysian financial organizations. It includes sources, such as production and disaster recovery sites, outsourced data centers, and even the cloud-based databases that fall under RMiT guidelines.
- RMiT Domains
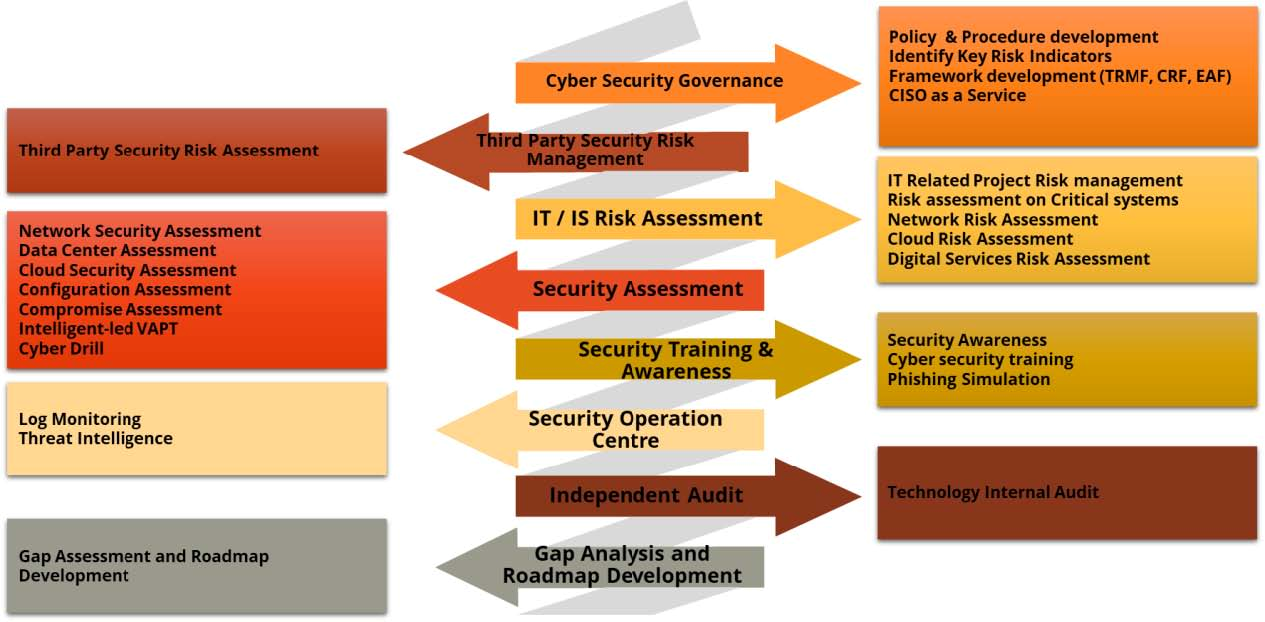
Check out the image depicting multiple RMiT domains:
What Is the Purpose of the RMiT Framework?
The security breaches in financial institutions lead to huge economic losses, disrupted business operations, and reputational damage. In such a situation, the best strategy is to prevent them before they could take place. Thus, Bank Negara Malaysia enforced Risk Management in Technology (RMiT) framework to ensure that the financial institutions build healthy cyberspace for their clients and customers while practicing the best risk management practices.
Repercussions
In case any Malaysian financial institution fails to comply with the RMiT framework, it will face –
- Failure in reducing and mitigating security risks, leading to serious financial implications.
- Ineffective risk handling, damaging organizational reputation to an irreparable extent
- Hefty fines and penalties
- Disruptions in internal processes, especially if they are complex and disorganized
- Inability to fight against existing and new threats
EGS team can help you comply with the RMiT framework’s regulations and avoid all the above-stated ill-effects.
Why EGS?
- We are a part of the world’s leading cybersecurity certification body, EC-Council.
- We can help organizations to achieve compliance with RMiT.
- We are committed to helping organizations prioritize efforts on critical systems.
- We can help organizations gain insight into the size and complexity of your operation
- We can help organizations reduce their exposure to cyber risks by fortifying their very own human firewall.
Our team of experts offers IT Risk Assessment services that help you locate the possible security risks and eliminate them. With our years of work in the industry, we know what kind of security solutions your financial organization needs to comply with regarding the RMiT framework.
In addition, EGS assigns a team of professionals onsite and can make a much broader team of exceptionally credentialed operational risk and resiliency experts available. Business continuity management, IT disaster recovery, emergency, and crisis management, cybersecurity forensics, and crisis media management strategy are at our client’s disposal if required.
Even more broadly, EGS is dedicated to helping organizations protect and enhance enterprise value in an increasingly complex legal, regulatory, and economic environment – with consulting professionals helping anticipate, illuminate and overcome complex business challenges. EGS has its reach and expert resources located globally to provide our clients with broader expertise in this area.
EC-Council Global Services can help you gain valuable insight into your operations’ size and complexity and fulfill the requirements of RMiT.
Our Methodology
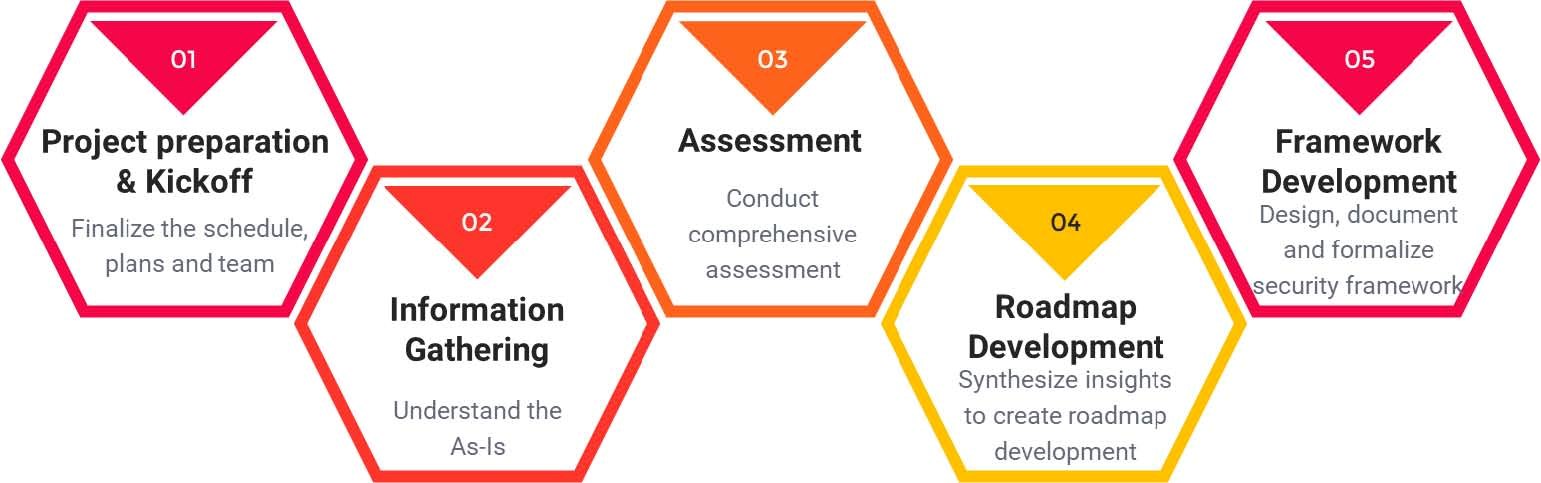
Our Roadmap to Achieve Compliance with RMiT
Below is the list of proposed deliverables for the engagement:
- Project Implementation Plan
- Project Organization Chart
- Technology Risk Management framework (TRMF) document
- Cyber Resilience Framework (CRF) document
- Enterprise Architecture Framework (EAF) document
- Gap analysis report with remedial actions
Our Experience
Some of our clients include:
- A well-known insurance service provider in Malaysia
- A multinational financial services company
- A major financial institution in Malaysia
We’re here to help!
Are you looking for more information? Or do you want to book a meeting?
Connect with an EGS Security Specialist
